Learning how to create strong passwords isn’t just good advice — it’s survival in the digital age. Every year, billions of credentials get leaked in data breaches, and the vast majority of those breaches start with weak, reused, or predictable passwords. If you’re still using your pet’s name plus “123” for every account, you’re handing hackers the keys to your digital life. This guide walks you through exactly how to build unbreakable passwords, why most people get it wrong, and how our password security tool makes the whole process painless.

[rank_math_toc]
Why Password Security Is More Important Than Ever
Here’s a number that should scare you: the average person has over 100 online accounts. How many of those share the same password? If you’re honest, probably most of them. It’s convenient — until one site gets breached and suddenly every account with that same email-password combo is vulnerable. For more on this topic, see our guide on secure password generator. For more on this topic, see our guide on free online text tools.
Cybercrime isn’t some niche threat anymore. According to the FBI’s Internet Crime Complaint Center, Americans lost over $12.5 billion to internet crime in a single year. A huge chunk of that starts with compromised passwords. Phishing attacks, credential stuffing, brute force attacks — they all exploit weak passwords.
The problem isn’t that people don’t care. It’s that creating and remembering strong passwords for dozens of accounts feels impossible. That’s exactly why we built our secure password generator and checker tool — to take the mental load off your plate and give you passwords that actually hold up against modern attack methods.
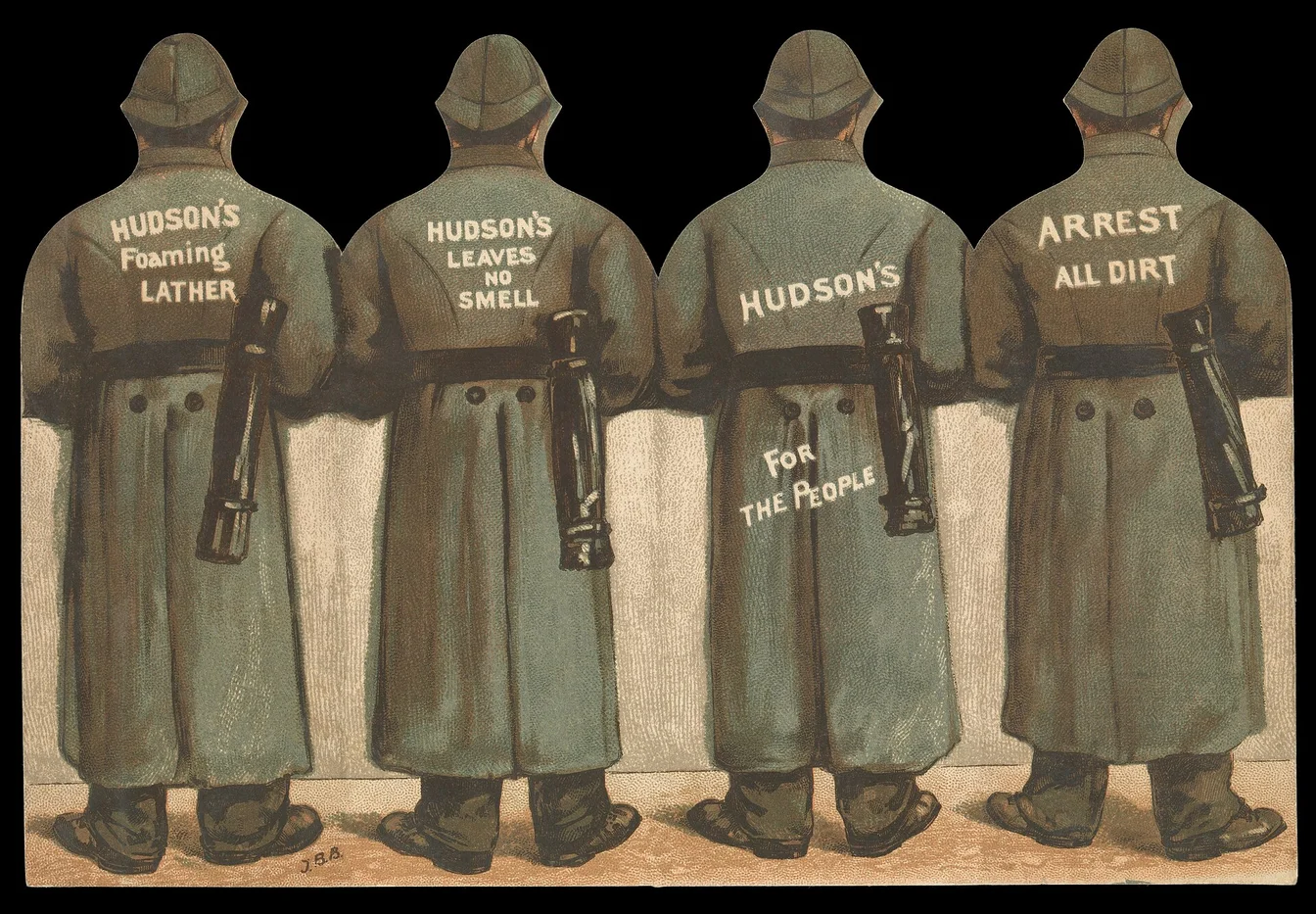
Image placeholder: Infographic showing password breach statistics — alt text: “Password security statistics showing data breach numbers and common password mistakes”
What Makes a Password Strong (And Why Most Fail)
Let’s break down what actually makes a password hard to crack. It’s not just about length, though that matters. It’s about entropy — the mathematical measure of how unpredictable your password is. The more entropy, the harder it is to guess, even with powerful computers running billions of attempts per second.
Length Matters Most
A 12-character password using only lowercase letters has about 56 bits of entropy. That sounds like a lot, but a modern GPU can crack it in hours. Now, bump it to 16 characters with mixed case, numbers, and symbols? You’re looking at over 95 bits of entropy. That would take a supercomputer thousands of years to brute force. Length is the single biggest factor in password strength, which is why passphrases (like “correct-horse-battery-staple”) have become so popular.
Complexity Adds Layers
Mixing uppercase letters, lowercase letters, numbers, and special characters multiplies the number of possible combinations exponentially. A password that uses all four character types is significantly stronger than one using just one or two, even at the same length. But here’s the catch: complexity only works if it’s random. “Password1!” uses all four types but would be cracked in under a second because it follows a predictable pattern.
Uniqueness Is Non-Negotiable
You could have the strongest password in the world, but if you use it for every account, you’re still extremely vulnerable. When (not if) one service gets breached, attackers will try that same email-password combination on every major platform. This is called credential stuffing, and it’s terrifyingly effective. Every single account needs its own unique password.
Common Password Mistakes You’re Probably Making
We’ve all been there. You need to create an account quickly, so you type something easy to remember and move on. Here are the mistakes that get people hacked:
Using personal information: Your birthday, your kid’s name, your hometown — these aren’t secrets. They’re on your social media profiles. Any attacker worth their salt will check your Facebook page before trying to guess your password.
Substituting numbers for letters: “P@ssw0rd” isn’t clever. Every password cracking tool knows this trick. The “leet speak” substitutions (3 for E, 0 for O, @ for A) add almost zero security because they’re so common.
Reusing passwords across accounts: We covered this, but it bears repeating. One breach compromises everything. According to NIST’s digital identity guidelines, password uniqueness is one of the most critical factors in overall security posture.
Using keyboard patterns: “qwerty,” “asdfgh,” “1q2w3e” — these are among the first things automated tools try. They’re not random; they’re predictable paths on a keyboard.
Making minor modifications: If your old password was “Sunshine1” and you changed it to “Sunshine2,” that’s not a new password. Attackers account for incremental changes.
Image placeholder: Visual showing weak vs. strong password examples — alt text: “Comparison of weak passwords versus strong passwords with security ratings”
How to Create Strong Passwords: Step-by-Step
You don’t need to be a cybersecurity expert to create strong passwords. Here’s a straightforward method that anyone can follow:
Step 1: Use a password generator. This is the easiest path. Our password creation tool generates cryptographically random passwords that meet the highest security standards. You choose the length and character types, and it handles the rest.
Step 2: Go long — 16 characters minimum. Longer passwords are exponentially harder to crack. If a site limits you to 12 characters, use all 12. But whenever possible, aim for 16 or more.
Step 3: Use all character types. Uppercase, lowercase, numbers, and symbols. Some sites don’t allow certain special characters, so our tool lets you customize which ones to include.
Step 4: Never reuse it. One password per account. No exceptions. If that sounds impossible to remember, that’s what password managers are for.
Step 5: Store it securely. Write it in a password manager, not on a sticky note. Not in a spreadsheet. Not in a text file on your desktop. Password managers encrypt your vault with a master password, so you only need to remember one strong password.
The Passphrase Method: An Alternative Approach
If you need a password you can actually remember (for your password manager’s master password, for example), consider using a passphrase instead. A passphrase is a string of random words separated by dashes or spaces. Something like “purple-ocean-calendar-sunset-breeze.”
Passphrases work because they’re long (which increases entropy) and memorable (because words are easier to recall than random characters). A five-word passphrase with a 7,000-word dictionary has roughly 61 bits of entropy — stronger than most 10-character complex passwords. And it’s way easier to type on a phone.
The key is randomness. Don’t pick words that form a sentence (“I love my dog Spot”). Pick truly random, unrelated words. You can use the EFF’s passphrase word list to generate random word combinations — it’s a trusted resource in the cybersecurity community.
Why You Need a Password Manager
Let’s be real: you’re not going to memorize 100+ unique, complex passwords. Nobody can. That’s where password managers come in. They generate, store, and auto-fill your passwords so you never have to type them manually.
Good password managers encrypt your vault with AES-256 encryption, which is the same standard used by banks and government agencies. They work across all your devices — phone, tablet, laptop — and most of them will alert you if any of your passwords appear in known data breaches.
If you’re building online tools and websites, security should be part of your workflow from day one. Check out our guide on high-CPM niches for AI tool websites to see how security tools fit into profitable site strategies.
Two-Factor Authentication: Your Backup Plan
Even the strongest password can be compromised. Phishing attacks are getting sophisticated enough to fool security professionals. That’s why two-factor authentication (2FA) is essential. It adds a second verification step — usually a code from an authenticator app or a biometric check — so even if someone steals your password, they still can’t access your account.
Enable 2FA on every account that supports it. Prioritize your email, banking, and social media accounts — those are the highest-value targets. Use an authenticator app (like Google Authenticator or Authy) rather than SMS codes when possible, since SMS can be intercepted through SIM-swapping attacks.
If you manage multiple online properties, like programmatic SEO websites, 2FA is especially critical because a compromised admin account could give attackers access to your entire portfolio.
Image placeholder: Diagram showing how two-factor authentication works — alt text: “Two-factor authentication flow diagram showing password and verification code steps”
What to Do If Your Password Gets Compromised
Despite your best efforts, breaches happen. Here’s what to do the moment you discover a compromised password:
1. Change it immediately. Don’t wait. Don’t think about it. Change it right now on the affected site.
2. Check other accounts. If you reused that password anywhere (and be honest with yourself), change those too. Every single one.
3. Enable 2FA. If you hadn’t already, turn on two-factor authentication for the compromised account and all related accounts.
4. Monitor for suspicious activity. Check your bank statements, email sent folders, and account settings for anything you didn’t do.
5. Use a breach checker. Tools like Have I Been Pwned let you check if your email has appeared in known data breaches. It’s free and takes seconds.
Frequently Asked Questions
How long should my password be?
Absolute minimum: 12 characters. Realistically: 16 or more. Every additional character exponentially increases the time it takes to crack your password. If a site allows long passwords, use them. A 20-character random password is virtually uncrackable with current technology.
Is it safe to use a password generator?
Yes, as long as you’re using a reputable tool. Our password generator creates cryptographically random passwords — meaning they’re generated using true random number generation, not predictable algorithms. The passwords are created locally and never stored or transmitted.
Should I change my passwords regularly?
NIST actually updated their guidelines to say you don’t need to change passwords on a regular schedule — only when there’s a reason to believe they’ve been compromised. Forced periodic changes often lead to weaker passwords because people make minor, predictable modifications. Focus on strength and uniqueness instead of rotation.
Are password managers really safe?
Nothing is 100% safe, but password managers are far safer than the alternative (reusing passwords or writing them down). The major password managers use zero-knowledge encryption, meaning even the company can’t access your passwords. A breach of their servers wouldn’t expose your vault without your master password.
What’s the difference between a password and a passphrase?
A password is typically a short string of random characters (like “K9#mP2$vL5@n”). A passphrase is a longer string of random words (like “blueberry-elephant-rocket-sunset”). Passphrases can be just as secure as complex passwords while being easier to remember and type, especially on mobile devices.
Can hackers really crack my password?
Yes, and faster than you think. A modern GPU can test billions of password combinations per second. A 6-character password using only lowercase letters can be cracked in under a second. Even an 8-character password with numbers and symbols typically falls within hours. That’s why length matters so much — a 16-character password with full complexity would take millions of years to brute force.
Disclaimer: This article is for educational purposes only. While we strive to provide accurate and up-to-date information about password security, cybersecurity threats evolve constantly. Always follow the latest security recommendations from trusted sources like NIST and your local cybersecurity agencies. Use the tools mentioned at your own discretion.